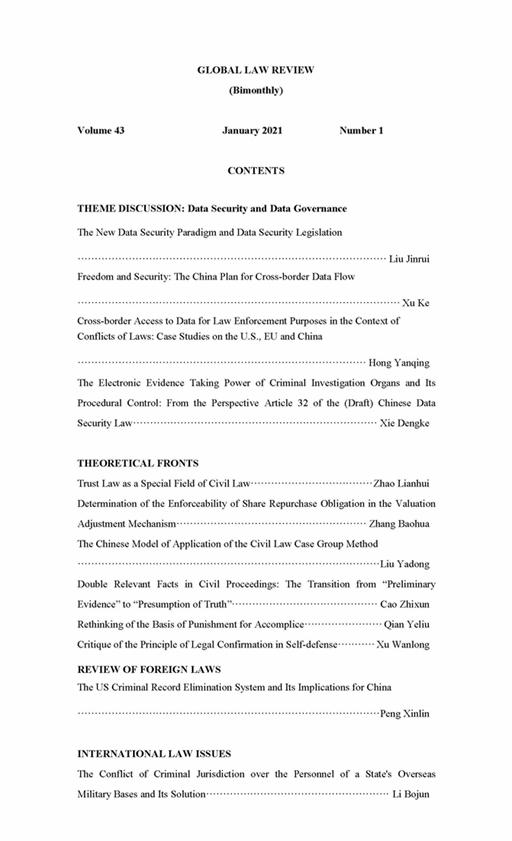
The New Data Security Paradigm and Data Security Legislation
Liu Jinrui
Abstract:The large-scale flow, aggregation and analysis of data in the era of digital economy have posed new risks and challenges that can no longer be addressed by traditional paradigms of information security and cyber-security and, as a result, a new paradigm is urgently needed to ensure data security. This article proposes a new data security paradigm centered on data security risk management: apart from confidentiality, integrity and availability of data security per se, this paradigm also tries to ensure the controllability and legitimacy of the security of data utilization. With respect to legislation on data security, China should carry out systematic design of data security legal system from the perspective of national security, construct the data security safeguard system by focusing on data security risk management, and control national security risk by taking important data protection as the core. In particular, the national data security management system should take important data as the key link, establish important data identification system, provide for data security protection obligations of important data processors, incorporate important data security review into the cyber-security review system, and establish the regulatory system for the transfer of important data out of the country.
Freedom and Security: The China Plan for Cross-border Data Flow
Xu Ke
Abstract: Currently, countries around the world have sharp differences on issues such as "should free flow be a principle of cross-border data flow" and "what is the justification for regulating cross-border data flow". China’s (Draft) Data Security Law puts forward for the first time the principle of safe and free flow of data, which takes the free flow of data as the basic principle and the safe flow of data as a restrictive principle, to balance the dual goals of opening up to the outside world and protecting national security and provide a prudent, inclusive, and cooperation-encouraging plan for global data governance. However, the conflict between free flow of data and safe flow of data will not disappear spontaneously by itself, because the solution of this conflict relies on the trade-off of different principles under different types of cross-border data flow. In the case of data flowing out of the country, the static security (integrity, availability and confidentiality of data) is the prerequisite for free flow of data, whereas the dynamic security (controllability of important data and credibility of non-important data) constitutes the hard and soft constraints on the free flow of data. In the case of data retrieval, China can retrieve important data from abroad on ground of controllability of important data. Meanwhile, based on the principle of reciprocity, China should also provide an institutionalized channel for other states to retrieve data from its territory.
Cross-border Access to Data for Law Enforcement Purposes in the Context of Conflicts of Laws: Case Studies on the U.S., EU and China
Hong Yanqing
Abstract: In the field of administrative and criminal law enforcement, the widespread use of information technology has made it common for evidentiary materials to exist in the form of electronic data. At the same time, globalization and digitization make it necessary for the cross-border access to data for law enforcement purposes, which exists in two main scenarios: first, when the data needed for domestic law enforcement in that country happens to be stored abroad; and second, when foreign law enforcement agencies need to access data stored in that country. Therefore, a government often has the need to "take" data from abroad and "prevent" data from being taken by foreign governments. As major players in the digital economy, the U.S. and EU have adopted different models of "taking" and "preventing" regarding the cross-border data access for law enforcement purposes on the basis of their respective practical needs, industrial development, legal traditions and overall strategies. In recent years, with the advancement in the making of the International Criminal Justice Assistance Law, the Data Security Law, the Personal Information Protection Law and related departmental rules, China is gradually developing a legal system of cross-border data access for law enforcement purposes with its unique style. This paper analyzes and summarizes the three different models of cross-border data access for law enforcement purposes, namely the US model, the EU model and Chinese model, predicts the possible results of the interactions between the three models, and analyzes their impact on China's sovereignty, security, and development interests.
The Electronic Evidence Taking Power of Criminal Investigation Organs and Its Procedural Control: From the Perspective Article 32 of the (Draft) Chinese Data Security Law
Xie Dengke
Abstract: Article 32 of the (Draft) Chinese Data Security Law lays down rules on the subjects, purposes and approval procedure of electronic evidence taking at the legislative level for the first time in China. As such, it is of great significant to bringing electronic evidence taking under the rule of law in China. Under this article, electronic evidence taking must go through strict approval procedure. As far as its legal nature is concerned, electronic evidence taking is a compulsory investigation measure similar to technical investigation, which is in contradiction with existing judicial interpretations and departmental rules in China. Therefore, it’s necessary to clarify the legal nature of electronic evidence taking and that of the legal rules on electronic evidence taking. As the “king of evidence” in judicial cases in the Internet and information age, electronic evidence is different from traditional physical evidence in both the form and the evidence taking mode, resulting in the triple paradox in traditional criminal procedure law and its application in electronic evidence taking. In constructing the electronic evidence taking system under the Data Security Law, China should not only consider the legal nature of electronic evidence taking and maintain its coherence with the existing criminal procedure law and evidence law, but also lay down procedural protection measures adapted to the characteristics of electronic evidence itself.
Trust Law as a Special Field of Civil Law
Zhao Lianhui
Abstract: Trust law, as an imported product from common law countries, is a flexible, convenient and universal legal system. In order for it to take root in China, the problem of its integration and coordination with local civil and commercial law institutions must be gradually solved. Trust law is a special field of civil law. Although it challenges the boundary of traditional civil law, it is essentially a civil law institution. Since the introduction of the trust legal system into China, the Chinese academic and practical circles have been continuously interpreting and questioning from various perspectives the system itself and institutional soil on which it depends for its survival. This paper discusses the survival of trust law in China, the particularity of trust relationship as fiduciary relationship (legal relationship), the possibility of the structure of trust property right being compatible with Chinese legal system (property right), the relationship between trust and civil entity law and organizational law (entity law and organizational law), the special remedies (civil liabilities and remedies) provided by trust law and other basic theoretical issues, with a view to demonstrating the essential characteristics of trust law as a special civil law.
Determination of the Enforceability of Share Repurchase Obligation in the Valuation Adjustment Mechanism
Zhang Baohua
Abstract: The share repurchase obligation in the valuation adjustment mechanism is a kind of obligation that takes the payment of share repurchase fund as its content, and the essence of the enforceability of the share repurchase obligation is the limitation of fund source of share repurchase. The enforceability of contract should be confirmed to the maximum extent under the precondition of holding the bottom line of creditor protection. If performing the repurchase obligation would cause the target company to violate the mandatory norm of creditor protection, the legal impossibility of performance can be established. The identification of the source of repurchase funds needs to fully comply with the general rules of debt performance under the contract law as well the special norms on share repurchase and other matters under the company law. In the case of non-capital reduction, depending on the explanation of the fund restriction on share repurchase, even the reserve funds and other legitimate funds can be used for repurchase payment in addition to proceeds of transferring share and the distributable profits. In the case of capital reduction, as long as the target company can meet the requirements of creditor protection, there is no performance obstacle. The completion of capital reduction is not the necessary condition of the fulfillment of share repurchase obligation by the target company. The target company should bear the burden of proof for impossibility of performance. The enforceability of the obligation of share repurchase should be determined in light of the company’s financial situation, and partial performance, performance by installments and deferred performance should be taken as possible judgment options.
The Chinese Model of Application of the Civil Law Case Group Method
Liu Yadong
Abstract: The case group method of civil law is a very important legal method in the methodology of civil law, which is widely applied to the uncertain legal concepts and general clauses in civil law. However, there are two theoretical obstacles to the application of this method in China: one is that the binding force of precedents as the basis of comparison is doubtful in the sense of source of law; the other is that the alternative elements formed by case groups are not normative. In China's judicial system and source of law system, theoretical obstacles to the application of civil law case group method can be overcome by two approaches: one is selecting precedents as guiding cases to solve the problem with the binding force of precedents, so that the case group thus formed becomes normative; the other is enabling the case group formed by other similar cases to evolve into customary law and thus become normative. The concrete development of civil law case group method can be divided into two steps: firstly, to obtain the rules of judge law as the basis of comparison; secondly, to form a case group through similarity judgment, and then to abstract the alternative elements.
Double Relevant Facts in Civil Proceedings: The Transition from “Preliminary Evidence” to “Presumption of Truth”
Cao Zhixun
Abstract:Factual allegations, which are essential for both the substantive success and procedural requirements of a civil case, have particularity in civil process. In the trial of ordinary civil cases and intellectual property cases, courts often take the test of preliminary evidence as the trial criterion in the procedural phase of jurisdictional objection. Different from the preliminary evidence required in substantive trial, this criterion is defective because of its ambiguity. In comparison, the German law tends to adopt a theory of double relevant facts. This theory simplifies the procedural determination of relevant facts by presuming them to be true during the review of procedural preconditions of the civil litigation. Similar approaches have also been adopted in other jurisdictions. The protection of the defendant’s interests, the emphasis on procedural preconditions and the comparison between the procedural effects of different tests all call for a shift from preliminary evidences to the presumption of truth under Chinese law. China should improve the institutional design of presumption of truth and the supporting procedures in light of foreign experience and its own legal tradition.
Rethinking of the Basis of Punishment for Accomplice
Qian Yeliu
Abstract: The liability accomplice theory and the illegality accomplice theory have both reduced their relevance to legal interest infringement. As a result, the analysis of the basis of punishment for accomplice through the application of these two theories would not only meet with difficulties in obtaining doctrinal basis, but also cause unreasonable expansion of the punishment scope of the accomplice. The causality accomplice theory seeks the basis of punishment in the causality between one's own behavior and the illegal result, which is methodologically appropriate. Within the causality accomplice theory, the pure causing theory goes beyond the definitive framework of the benchmark of constituent elements and contravenes the principle of a legally prescribed punishment for a specified crime. Moreover, it negates accomplice illegality’s dependence on principal offender illegality, thus improperly expands the scope of punishment for the accomplice. Both mixed causing theory and revised causing theory affirm that the accomplice’s illegality depends on the principal offender’s illegality, and adhere to the limited dependency theory. Under this premise, the revised causing theory adheres to the absolute connection of illegality between accomplices, while the mixed causing theory proposes that, if the principal offender has a cause of illegality elimination, the illegality of the accomplice will exceptionally be denied. In comparison, the mixed causing theory is more appropriate because it admits the relativity of illegality exceptionally. Adhering to the mixed causing theory is conducive to the rational determination of special types of criminal participation.
Critique of the Principle of Legal Confirmation in Self-defense
Xu Wanlong
Abstract:Currently the principle of legal confirmation is gaining popularity in the academic and practical circles in China. However, at the conceptual level, the principle of legal confirmation cannot be explained from the perspectives of “the maintenance of the actual effect of legal order”, “the maintenance of the normative effect of legal order” or “general prevention”. The basic proposition of the principle, namely “the legal order is the supreme interest”, is also invalid. At the logical level, the principle has such problems as circular argument, self-contradiction and logic break. At the level of legal doctrine foundation, the “principle of superior interest” and the “representative doctrine”, on which the principle of legal confirmation is based, are untenable. The principle of superior interest is only a formal principle that cannot be self-sufficient. The problem with the “representative doctrine” is that the necessary conditions for private individuals to perform tasks of the state as its representatives do not exist in the case of defense. In addition, if the defender is really a representative of the state, he shall also be restricted by the principle of proportionality. To sum up, the principle of legal confirmation should not be the legal doctrine foundation of self-defense in China.
The US Criminal Record Elimination System and Its Implications for China
Peng Xinlin
Abstract: The US criminal record elimination system is the most representative one in Western countries. The US position on the elimination of criminal records has been clearly affected by criminal policies in different periods of time. Although the system under the federal law and those under the laws of various states are different, most of them impose restrictions on the elimination of criminal records, and basically allow the elimination of juvenile criminal records, the criminal records of defendants whose cases have not been closed with a judgment, and the criminal records of defendants in wrongly judged cases. There are mainly three modes of initiating the criminal record elimination procedure: initiation at the request of the applicant, initiation by the judicial authority and initiation according to the government's amnesty order. The embodiments of the legal effect of elimination of criminal record are mainly reflected in four aspects: deletion or sealing up of criminal records; not regarding the denial of the criminal records as constituting the crime of perjury; prohibiting the relevant stakeholders from inquiring about the eliminated criminal records; and recovery of rights. In drawing on the rule of law experience of elimination of criminal record in the US, China should reconcile the related value conflicts, build a full coverage system, establish a reasonable mode, broaden the content of the system, and improve the safeguard measures.
The Conflict of Criminal Jurisdiction over the Personnel of a State's Overseas Military Bases and Its Solution
Li Bojun
Abstract: In international law, the exercise of criminal jurisdiction by a state within or outside its territory is the most direct embodiment of its exercise of sovereignty. Since the end of the Second World War, with the increase in the exchange between states and in the transnational mobility of personnel, conflicts of criminal jurisdiction have been increasing, and the question of how sovereign states coordinate and resolve such conflicts in their international relations has become increasingly prominent. In particular, the general international law does not provide a clear solution to conflicts arising from the criminal jurisdiction over the personnel of a state's overseas military bases. The states concerned generally resolve this issue by concluding status-of-forces agreements. However, due to the profound influence of the principle of territorial sovereignty, the exclusive criminal jurisdiction of the base-sending states over the personnel of their overseas military bases in accordance with the principle of flag state law is subject to more and more restrictions by the laws of the base-receiving states. Therefore, the settlement of the conflict of criminal jurisdiction over personnel in overseas military bases mainly involves the coordination and distribution of the territorial criminal jurisdictions between the receiving state and the sending state.



